Iran Hackers Target US: Cyberattack Risk Soars Amid War
Iran-linked cyberattacks are targeting US infrastructure and allies, escalating digital warfare risks during ongoing Middle East conflicts. Pro-Iranian hacking groups have claimed responsibility for major attacks on American companies, including medical device manufacturer Stryker, while expanding their operations across critical sectors.
⚡ Quick Summary
- Iran-backed hackers attacked US medical company Stryker and multiple regional targets
- Cybercriminals targeting defense contractors, power stations, and water facilities
- Digital warfare strategy aims to disrupt American war efforts and increase costs
- Attacks span across Israel, Saudi Arabia, Kuwait, and expanding into US territory
What Are Iran-Linked Cyberattacks?
Iran-linked cyberattacks are defined as coordinated digital operations conducted by hacking groups affiliated with or supported by the Iranian government. These sophisticated cyber operations target critical infrastructure, government systems, and private companies across multiple countries to advance Iran’s geopolitical objectives and weaken adversaries’ capabilities.
Latest Cyberattack Developments
On Wednesday, pro-Iranian hackers successfully penetrated systems belonging to Stryker Corporation, a Michigan-based medical device manufacturer, marking a significant escalation in targeting American companies. This attack represents part of a broader campaign that began intensifying on February 28, 2024.
The hacking groups have systematically targeted surveillance cameras across Middle Eastern nations to enhance Iran’s missile targeting capabilities. Additional targets include regional data centers, Israeli industrial facilities, educational institutions in Saudi Arabia, and transportation infrastructure in Kuwait.
According to cybersecurity firm Mandiant’s founder Kevin Mandia, “Something is going to happen because the gloves are off,” highlighting the unprecedented nature of current United States News cyber threats.
How Iranian Cyber Operations Function
Iranian cyber warfare operates through a multi-layered approach combining state-sponsored groups with affiliated proxy organizations. These operations typically involve:
- Intelligence Gathering: Penetrating surveillance systems and communications networks
- Infrastructure Disruption: Targeting power grids, water treatment facilities, and transportation systems
- Economic Warfare: Attacking defense contractors and major corporations
- Political Interference: Previous operations included infiltrating presidential campaign email systems
Impact on Critical Infrastructure and Defense Sectors
The primary objective of these Iran-linked cyberattacks involves systematically degrading American military capabilities and economic stability. Target priorities include:
Defense and Military Targets
Iranian hackers have repeatedly attempted to breach networks used by military personnel and defense contractors. These attacks aim to steal sensitive information, disrupt operations, and compromise national security systems.
Energy and Utilities Infrastructure
Power stations and water treatment plants represent high-value targets for Iranian cyber operations. Successful attacks could cause widespread blackouts, contaminate water supplies, and create public health emergencies.
Healthcare and Medical Systems
The Stryker attack demonstrates Iran’s willingness to target healthcare infrastructure, potentially affecting patient care and medical device functionality across hospital networks.
Strategic Objectives and Global Implications
Iranian cyber strategy focuses on achieving multiple strategic objectives simultaneously. These operations aim to increase the costs of American military involvement, strain cybersecurity resources, and cause maximum economic disruption to companies supporting defense initiatives.
Regional allies and partners face similar threats, with attacks documented across the Middle East targeting both government and private sector organizations. The scope of these operations suggests coordination with other state actors and terrorist organizations.
International Technology experts warn that additional Iranian allies joining current conflicts could exponentially increase cyber threat levels globally.
Defense Measures and Response Strategies
Government agencies and private organizations have implemented enhanced cybersecurity protocols in response to escalating Iranian cyber threats. Key defensive strategies include:
- Network Segmentation: Isolating critical systems from internet-connected networks
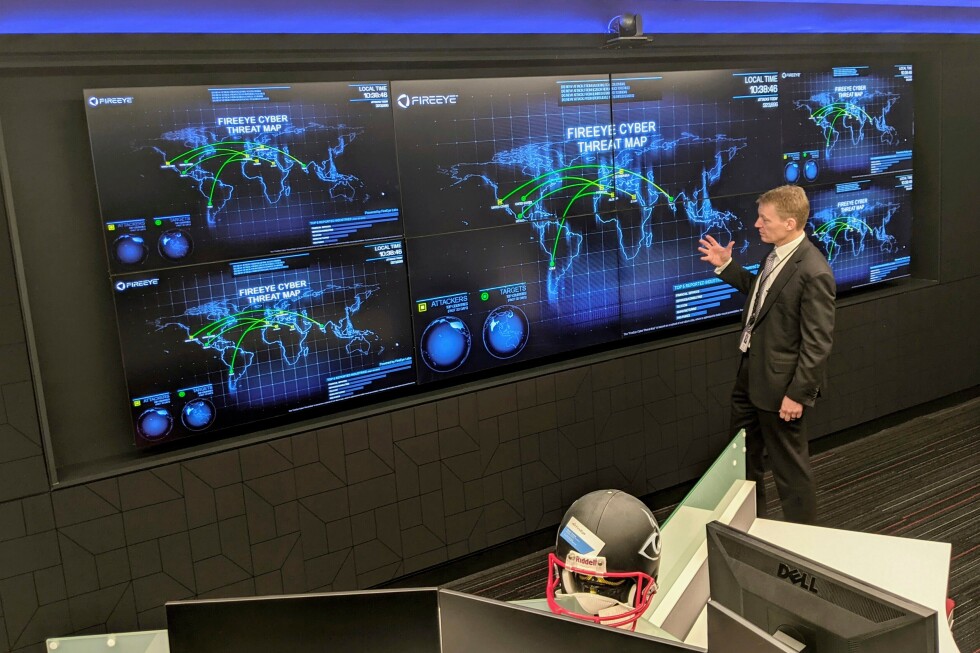
- Enhanced Monitoring: 24/7 surveillance of network traffic and system anomalies
- Incident Response Teams: Rapid deployment capabilities for cyber attack mitigation
- Intelligence Sharing: Coordination between government agencies and private sector partners
- Employee Training: Regular cybersecurity awareness programs and simulated attacks
| Target Sector | Risk Level | Primary Concerns |
|---|---|---|
| Defense Contractors | Critical | Classified information theft |
| Power Infrastructure | High | Grid disruption, blackouts |
| Healthcare Systems | High | Patient data, device manipulation |
| Water Treatment | Moderate | Supply contamination risks |
Frequently Asked Questions
What makes Iranian cyberattacks different from other state-sponsored attacks?
Iranian cyberattacks typically focus on causing maximum disruption and economic damage rather than traditional espionage. They often target civilian infrastructure and use proxy groups to maintain plausible deniability.
How can businesses protect themselves from Iranian cyber threats?
Companies should implement comprehensive cybersecurity frameworks including network monitoring, employee training, regular security audits, and incident response plans. Collaboration with government cybersecurity agencies provides additional threat intelligence.
Which industries are most at risk from Iranian hackers?
Defense contractors, energy companies, healthcare organizations, water utilities, and technology firms supporting government operations face the highest risk levels from Iranian cyber operations.
How do Iranian hackers typically gain access to target systems?
Common attack vectors include phishing emails, exploitation of software vulnerabilities, supply chain compromises, and social engineering tactics targeting employees with system access.
What should organizations do if they suspect an Iranian cyberattack?
Immediately isolate affected systems, contact cybersecurity authorities, preserve evidence for investigation, and activate incident response protocols. Report attacks to relevant government agencies for threat intelligence sharing.
Recent developments in Economy & Business sectors show increasing collaboration between cybersecurity firms and government agencies to address these evolving threats.
📚 Related Articles You May Like
Conclusion and Security Recommendations
Iran-linked cyberattacks represent a growing threat to American infrastructure and international security. The recent attack on Stryker Corporation demonstrates the expanding scope of Iranian cyber operations beyond traditional military targets.
Organizations must prioritize cybersecurity investments and maintain constant vigilance against evolving threats. Government agencies, private companies, and international partners must strengthen cooperation to effectively counter Iranian cyber warfare capabilities.
Stay informed about the latest cybersecurity developments and United States News by following our comprehensive coverage of international security issues.